ICT Documents
Cosa dicono norme & standard
-
DORA (UE 2022/2554): richiede un ICT Risk Management Framework, una Digital Operational Resilience Strategy (DORS), Incident Management (incl. classificazione/notifiche), Business Continuity & DR, Testing program (DORT), Third-Party/Outsourcing con Information Register, governance e reporting.
-
CSSF 22/806 (e circolari collegate): specifica governance ICT, outsourcing (contratti/clausole, registro, notifiche), BCM/DR, risk assessment, change/access ecc.
-
ISO/IEC 27001:2022: richiede Information Security Policy e controlli documentati (Annex A) per accessi, controllo cambi, backup, logging, cifratura, supplier security, sviluppo sicuro ecc.
-
GDPR: impone Data Privacy Policy, Data Classification & Handling, DPIA, registro trattamenti.
Baseline “must-have” (nel tuo contesto)
Queste sono le policy/procedure che ti consiglio come set minimo (aspettativa tipica di audit DORA/CSSF/ISO):
-
Information Security Policy
-
ICT Risk Management Framework Policy (+ ICT Risk Assessment Policy)
-
Digital Operational Resilience Strategy (DORS)
-
Incident Response Policy/Procedure (con classificazione e notifiche regulatory)
-
Business Continuity & Disaster Recovery Policy (BIA, test, RTO/RPO)
-
Access Management / IAM Policy (JML, review, privilegi)
-
Change Management Charter/Procedure
-
Vulnerability & Patch Management Policy/Procedure
-
Encryption/Cryptography Policy
-
Third-Party/Outsourcing Policy (+ Information Register DORA)
-
KRI Monitoring Policy (Appetite/Tolerance/Capacity + escalation)
-
Security Testing / DORT Program
-
Acceptable Use Policy (AUP)
-
Data Classification & Handling Policy
-
Backup & Restore Policy/Standard
-
Logging & Monitoring / SIEM Standard
-
Data Privacy Policy (GDPR, con DPO)
Regolamentate/di supporto (spesso richieste)
-
Value Chain / CIF Policy (perimetro CIF e mappatura dipendenze)
-
ICT Project Risk Management + Project Risk Assessment Methodology
-
Cloud/SaaS & Supplier Security Standard
-
Secure SDLC / DevSecOps Standard
-
Remote Work / Mobile Device / Email & DLP Standards
-
Physical & Environmental Security Standard
-
AI Governance/Policy (in arrivo lato gruppo)
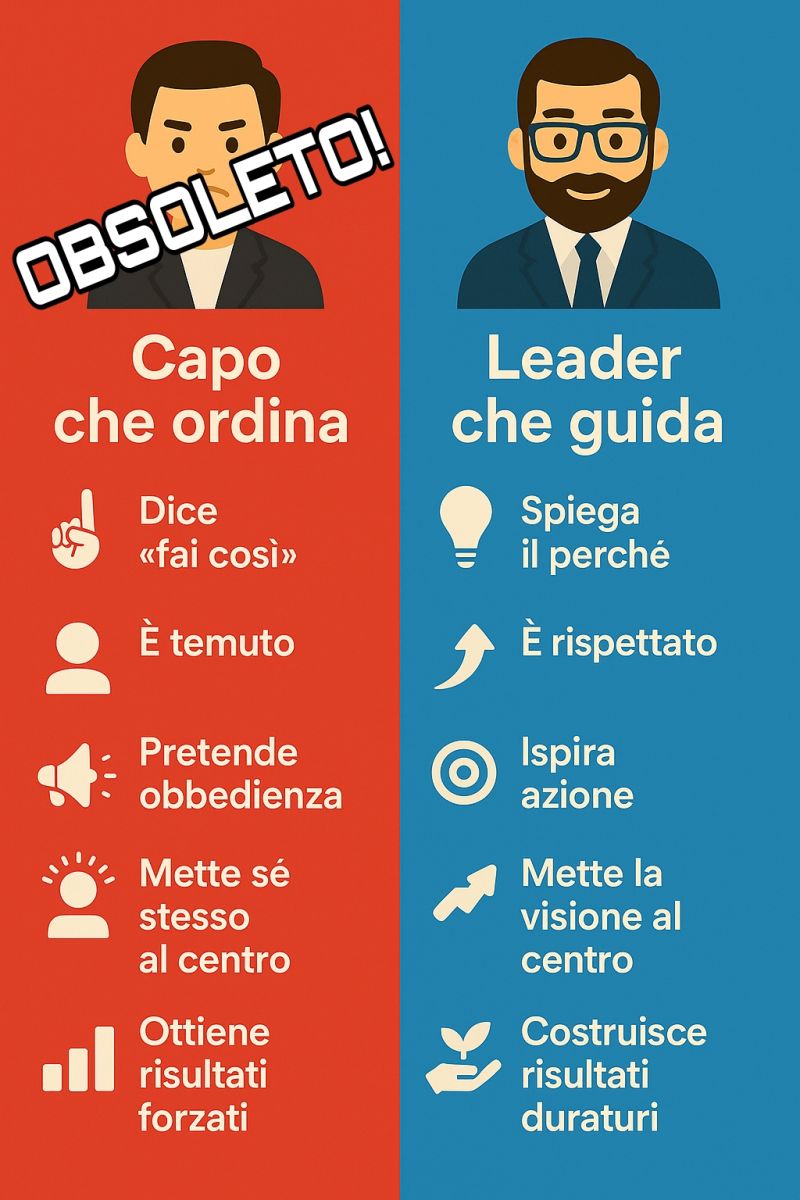
Copiato da linkedin
test
Headscale
docker compose up -d
docker ps
docker exec -it headscale headscale users create msolci
https://tailscale.com/kb/1031/install-linux
— sul client linux
curl -fsSL https://tailscale.com/install.sh | sh
tailscale up –login-server http://mail.saic.it:8585
— su server headscale
docker exec -it headscale headscale nodes register –user usolci –key [chiave macchina ottenuta prima]
docker exec -it headscale headscale nodes list
services:
headscale:
image: docker.io/headscale/headscale:latest
restart: unless-stopped
container_name: headscale
ports:
– “0.0.0.0:8585:8080”
– “0.0.0.0:9191:9090”
volumes:
– ./config:/etc/headscale
– ./lib:/var/lib/headscale
– ./run:/var/run/headscale
command: serve
heascale-ui:
image: ghcr/gurucomputing/headscale-ui:latest
container_name: headscale-ui
restart: unless-stopped
environment:
– HTTP_PORT=8080
ports:
– “8586:8080”
docker exec -it headscale headscale apikeys create
tailscale up –login-server http://headscale.saic.it:8585 –advertise-routes=192.168.X.0/24 –advertise-exit-node
docker stop $(docker ps -q)
docker compose stop
docker-compose down
